Listen to the article
The ongoing war in Ukraine has taken a dramatic turn in the digital realm, with Ukrainian intelligence claiming a major cyberattack on the servers of Russia’s Defence Ministry. This bold move, if confirmed, could be a game-changer, potentially offering Ukraine a significant advantage in the conflict.
According to the Ukrainian Defence Intelligence Unit (DIU), their cyber specialists managed to breach the heavily fortified digital defences of the Russian Ministry, gaining access to a vast amount of data. While the full extent of the information retrieved remains undisclosed, the DIU claims to have obtained:
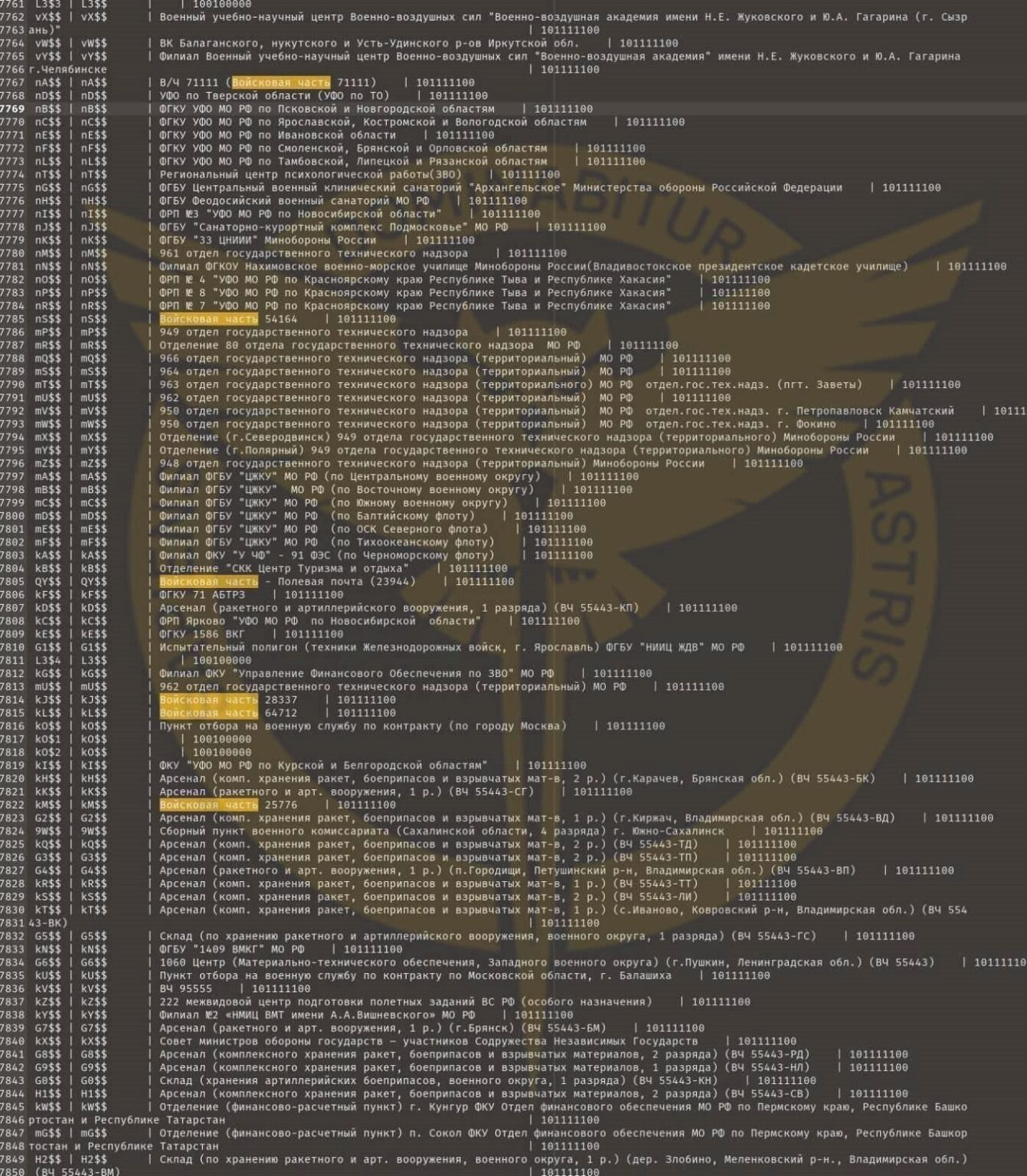
- Encryption Software: Access to sophisticated encryption software used by the Russian military, unveiling their cryptographic methods.
- Classified Documents: A trove of classified orders, reports, and communications, shedding light on the internal workings of the Russian Ministry of Defence.
- Structural Analysis: Insights into the complete structure of the Russian Ministry of Defence and its units, enhancing Ukraine’s strategic understanding.
- Identification of Officials: Identification of high-ranking officials, including generals and deputies, providing valuable intelligence on key decision-makers.
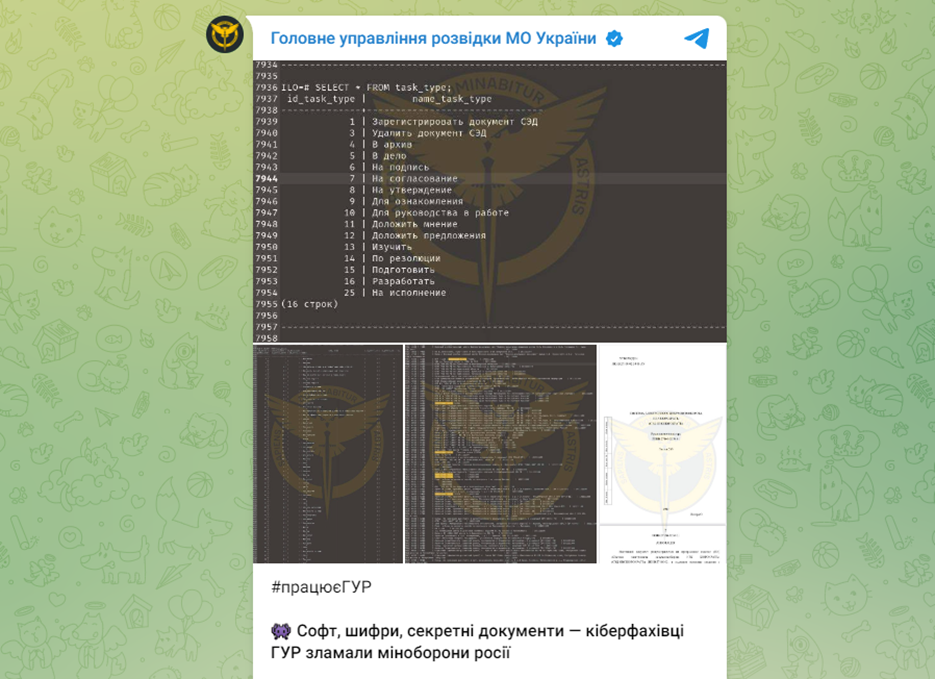
- Electronic Document Management Software: Unveiling the use of a specific software, “bureaucrat,” for electronic document management within the Russian military.
A Notable Target and a Special Thanks
One of the recognised individuals is Timur Vadimovich Ivanov, Russia’s Deputy Minister of Defence. Allegedly, Ukrainian military intelligence gained access to documents owned by Ivanov. Ivanov is a sanctioned individual and appears on the Anti-Corruption list of bribe-takers and warmongers, as he is implicated in corruption schemes related to construction activities in the territories of Ukraine occupied by Russia.
In their telegram post announcing the hack, the DIU conveyed gratitude to Russia’s Defence Minister Sergei Shoigu without delving into specifics, employing a handshake emoji and stating, “🤝 This deputy shoiju played an important role in making the cyber attack a success.” Suggesting that he might have been a vulnerability or a strategic point of exploitation in their operation.
The telegram message concluded with a statement affirming Ukraine’s ongoing efforts, “The work in Russian cyberspace aimed at obstructing and paralysing the activities of law enforcement agencies and officials of the aggressor state responsible for the war against the Ukrainian people continues.”
The successful cyber operation orchestrated by the Ukrainian DIU stands as a noteworthy milestone in the enduring conflict between Ukraine and Russia. This breach has yielded invaluable insights into the inner workings of the Russian Ministry of Defence, granting Ukrainian authorities a profound understanding of the organisation’s structure, key figures, and decision-making processes.
As the conflict continues, the role of cyber operations in shaping the strategic landscape is likely to become increasingly significant, with both sides leveraging technological advancements to gain an edge in the conflict.