Listen to the article
Against the backdrop of the ongoing war between Hamas and Israel, virtual soldiers have emerged, as the battle extends into the digital world. Digital warriors, aligned with various cyber groups, are now actively engaged in supporting their chosen sides in this escalating cyber conflict.
Israel, often acknowledged as a cybersecurity powerhouse and home to some of the globe’s leading digital defence firms, presents a formidable challenge for anyone trying to undermine its digital infrastructure. However, this status has not deterred determined hackers from attempting to disrupt Israel’s online presence, as evidenced by recent attacks that targeted their news and government websites, successfully taking them offline.
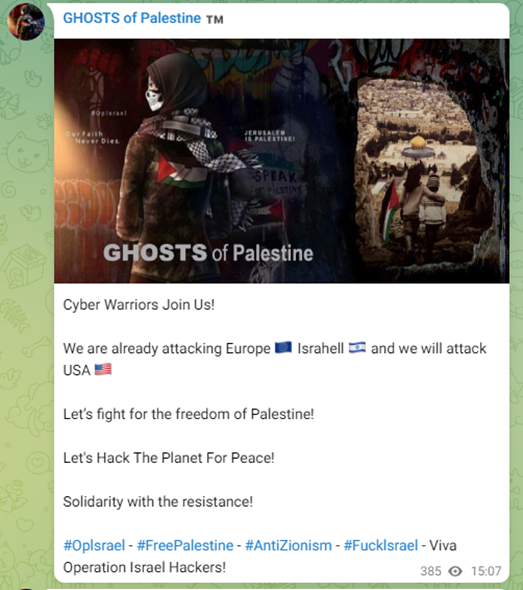
Pro-Palestine Hackers Target Key Services
Pro-Palestine hackers have primarily focused their cyber efforts on government websites, civil services, and critical infrastructure. Ghosts of Palestine, an anti-Israel group, has rallied hackers from across the globe under the banner of “hacking the planet for peace,” targeting multiple websites for takedowns and simultaneously releasing leaked Israeli data.
Cyber Av3ngers’ critical infrastructure attacks
Cyber Av3ngers, a pro-Palestine group, asserted that they had directed their efforts towards Israel’s DORAD power plant, successful hacking and disabling several of its production phases.
In addition, they claimed to have obtained confidential documents related to the facility. Although, Group-IB discovered that the data had actually been stolen by the ransomware group MosesStaff back in 2022, highlighting a recurring pattern wherein hacktivists attempt to generate attention by sharing data from prior attacks and presenting them as current, all in a bid to attract attention.
Still, cyber-attacks against Israel’s critical infrastructure continue to intensify, Cyber Av3ngers added Israel’s water company to the list. As Israel cut off the supply of water, electricity and food to the Gaza strip.
Cyber Av3ngers responded with “an eye for an eye” in a video they posted which shows they have accessed Israel’s water infrastructure, ending with the text “the worst is yet to come.”

AnonGhost’s Fake Nuclear War
AnonGhost exploited a weakness in the RedAlert app, which warns people in Israel about rocket attacks. They managed to use this weakness to get access to the app’s inner workings and then used special computer programs to send unwanted messages to some users of the app, sending messages about fake “nuclear bombs”.
AnonGhost also warned that “there will be surprises for the Israeli Cyber Security in the coming days.”
Russia’s KillNet targets Israeli websites
Russian hackers, believed to be under Kremlin control, have successfully breached Israeli government websites.
The hacktivist group KillNet has claimed responsibility for targeting all government systems in Israel, citing the Israeli government’s alleged support for Ukraine’s regime as motivation for their attacks.
“Israeli government, you are responsible for this bloodshed. Back in 2022, you supported the terrorist regime in Ukraine. You betrayed Russia.”
“Today, Killnet officially informs you of this! All government systems of Israel will be subject to our attacks!” was posted to the group’s Telegram channel.
Following KillNet’s announcement, the main Israeli government website was taken down.
Anonymous Sudan
KillNet has also announced collaboration with Anonymous Sudan, prolific hacktivist group, further complicating the cyber conflict landscape, which could increase the scale and intensity of attacks against Israeli targets.
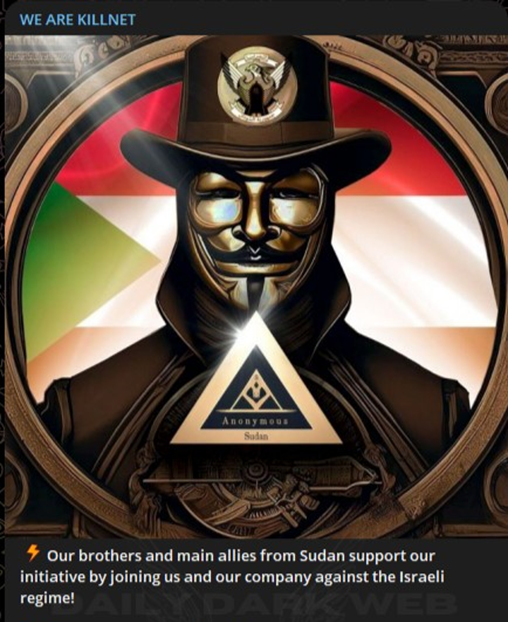
While Anonymous Sudan has previously denied having Russian origins, claiming to be Sudanese, Cyfirma highlighted that the majority of the group’s social media posts are written in Russian. Cyfirma pointed out that the group exhibits a level of geopolitical understanding not typically associated with Sudan, which is often exploited by actors affiliated with Wagner-affiliated troll factories.
Anonymous Sudan claimed to have taken aim at Israel’s critical Iron Dome missile defence system.

They also targeted The Jerusalem Post’s website causing it to go offline. Editor Avi Mayer expressed the magazine’s ordeal, stating, “we’ve been targeted by a succession of devastating cyberattacks since the warfare started” on the morning of October 7th.
India’s cyber offensive in support of Israel
Simultaneously, supporters of Israel have rallied in the cyber arena, launching their own attacks against Hamas’ digital assets.
As “India is with Israel” trended on X on the day of the launch of the attacks, the Indian Cyber Force posted that they would launch cyber-attacks on Palestine starting from October 8th.
The following day, the Indian Cyber Force took down Palestine telecommunications company website, Palestine National Bank website, Palestine web mail government services and the Hamas official website, among others.
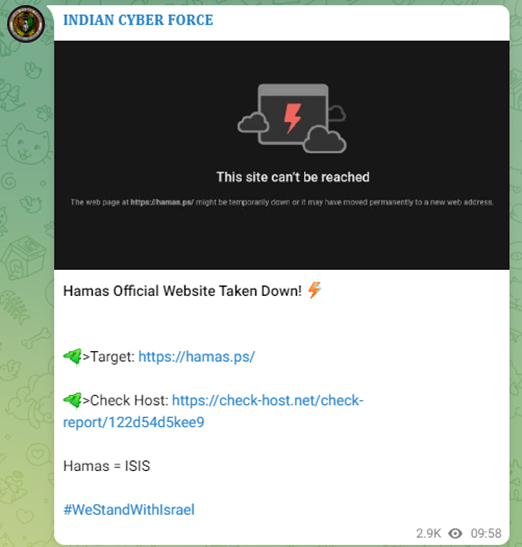
Other Indian hacktivists like SilentOne and Dark Cyber Warrior helped take down websites and hack network devices.
The involvement of Indian hacktivists saw several Indian governmental sites coming under fire.
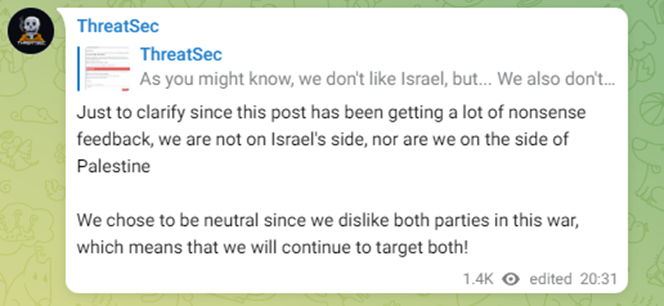
Others remained neutral
Hacktivist group ThreatSec has declared its neutrality in the conflict, but they did manage to breach and disable the Internet Service Provider (ISP) used in Palestine, effectively cutting off internet access for Hamas in Gaza.
ThreatSec claims to have “shut down every server” of AlFanet, which provides services to over 5,000 servers in the Gaza Strip.
They announced their success, “Our goal was just to get a hold of some infrastructure, but it turns out we actually have full control of the IP routing of over 5000 servers in the Gaza region, which means we can basically shut down everything that belongs to them. Isn’t that just lovely?”, posting this to their subscribers with the hashtag #StopWar.
ThreatSec then published another post emphasising their neutrality, even in the aftermath of the AlFanet attack.
As the Israel-Hamas conflict rages on, the ever-evolving battleground knows no bounds, drawing in nations far and wide as they grapple with the profound implications of the digital warfare.

